Week in OSINT #2023-19
Another packed episode, with topics ranging from fake news, to Telegram, and an old Chrome extension!
So much to talk about, and not everything made it into this week's episode, because I was a bit busy over the weekend. But I did manage to read a lot, and play with the Google Unlocked extension, and I am still happy that I'm able to write this Week in OSINT for close to five years, and keep on top of the OSINT news while doing it! Let's crack on, with the following topics:
- Inactive Twitter Accounts
- AI and Geolocation
- Telegram VM
- Fake Protesters
- New TLD
- Google Unlocked
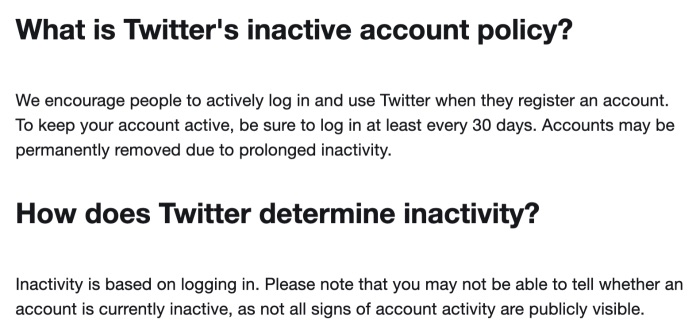
Tip: Inactive Twitter Accounts
Let's start with a warning about the new inactive account policy that was published on April 24 this year. The previous policy was published on September 13, 2019 and mentioned an inactive period of 6 months. I know from personal experience that Twitter didn't really act on this policy, since I still have a dormant account for a quiz out there. But if they are changing this policy, and are going to act on it, this might become a problem. Just think about investigators that actually hold dozens of accounts, and want to plan a long holiday...
Tip: AI and Geolocation
Henk van Ess shared some tips on how AI can be useful during investigative work. In this article he talks about generating lists of addresses, or coordinates. But what I found most interesting myself, is the last part of the post where Henk uses AI to find an address. By giving only partially available information, such platforms can easily return possible hits. At last, this is a use of ChatGPT for OSINT, that I think is absolutely great.
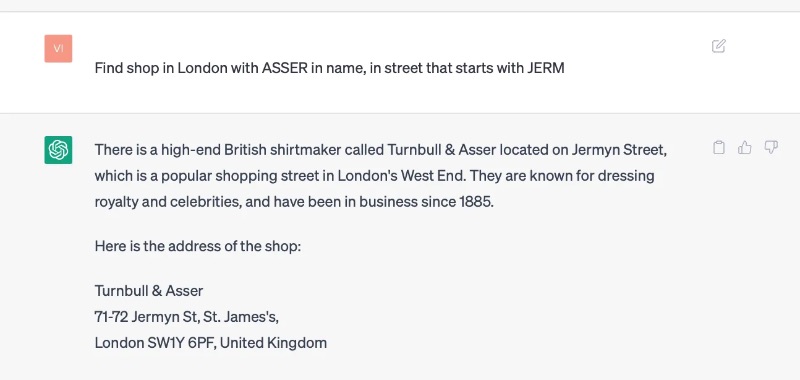
especially when one need to fill in the 'blanks'!
Link: https://www.digitaldigging.org/...
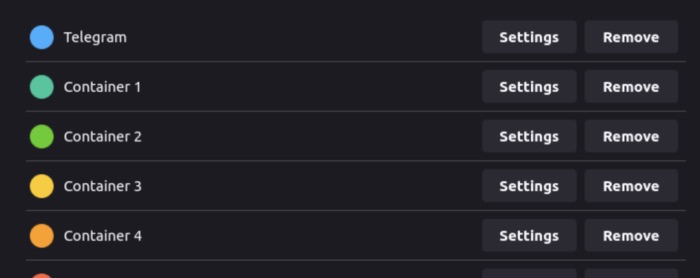
Tutorial: Telegram VM
Ginger T has posted a first part of a tutorial, where he describes how he built his Telegram VM. He takes the time to explain his language and VPN setup, why he uses containers in Firefox, and talks about his OpSec. He also talks in length about different settings in his browser, and the add-ons he uses in his VM. This is a wonderful tutorial for people that are new to setting up a VM, and I can't wait to read the second part!
Link: https://www.cqcore.uk/...
Article: Fake Protesters
Over the last few weeks journalists have uncovered a form of "fake news" I didn't see before. By sending people to genuine protests, but having them hold up signs that show pro-Russia and other messages, people were trying to be tricked into believing a different narrative. The photos that were taken of these 'protesters', had to make people believe there was more support than really was the case. An interesting investigation, and Twitter thread, by Kevin Shakir and his colleagues from the Danish DR Nyheder, Le Monde, Süddeutsche Zeitung, Westdeutscher Rundfunk, Norddeutscher Rundfunk, Expressen, NRK and SVT.

Article (DK): https://www.dr.dk/nyheder/...
Link: Twitter thread
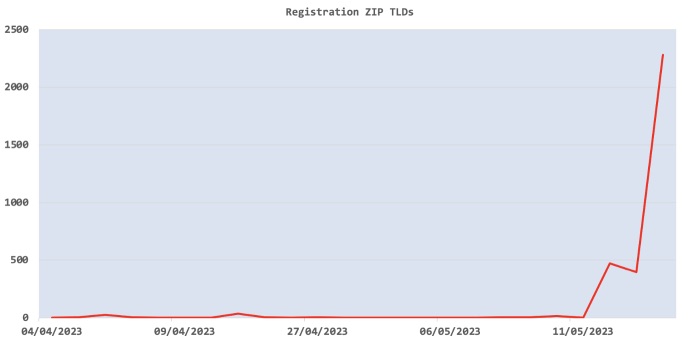
Tip: New TLD
Back in 2014 ICANN delegated a new TLD to their root servers, the top level domain .zip. Recently it became possible to register a domain name ending with this TLD, and many people did. This created quite an uproar in the InfoSec community, and I can understand why! When I looked into some of the most recent domain registrations, I found domains that could pose as legitimate programs of files. On May 12, the amount of registrations took a small leap, followed by an explosion of registrations on the May 14!
To give an example of the cesspool of domain names that were registered, I had a look at some very misleading domain names. All of these can easily be mistaken for a genuine file name:
| Date | Domain |
|---|---|
| 6 April | tumblr.zip, audible.zip |
| 19 April | facebook.zip, whatsapp.zip |
| 20 April | waze.zip, chromium.zip |
| 12 May | attachments.zip, document.zip |
| 13 May | vacationphotos.zip, windowsdrivers.zip |
| 14 May | office-update.zip, windowsupdate.zip |
| 15 may | attachement.zip, bankstatements.zip |
You want to keep an eye out for newly registered domains yourself? Or want to search for domains that might impersonate specific brands? Then do check out one of the best free sources our there, called DN Pedia. There you can see that on May 14, almost 2300 domain names were registered with this top level domain.
Link: https://dnpedia.com/
Tool: Google Unlocked
I received a tip about a new browser extension, called Google Unlocked. With this extension installed in Chrome or Firefox, it will be possible to see hidden, or removed, results directly in your browser. It works by looking for a response that contains a link to the Lumen Database on the bottom of the search page. The extension opens that page, and extracts all URL listed there, and places them on the bottom of the search results. Thanks for the share Exalt
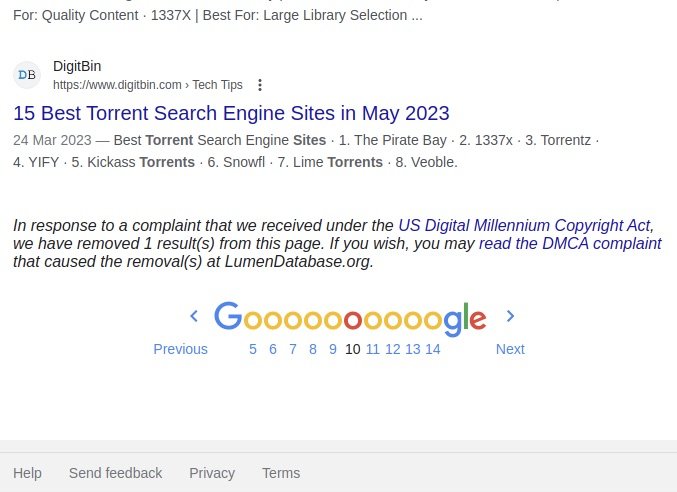 Before
Before
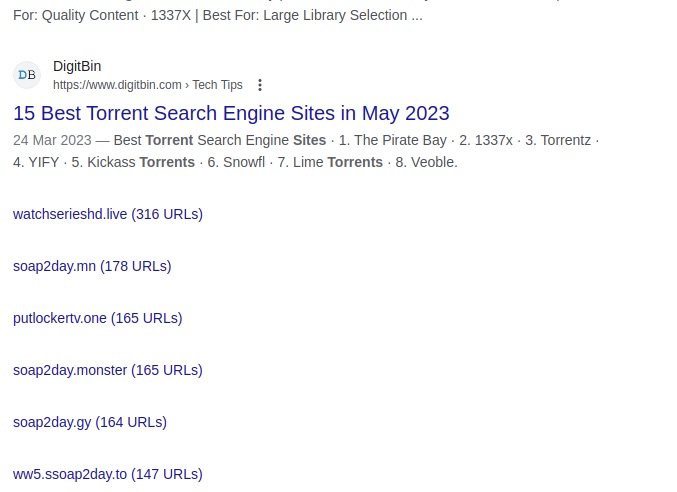 After
After
Link: https://github.com/Ibit-to/google-unlocked
Have a good week and have a good search!
