Week in OSINT #2022-02
Welcome to another Monday, your weekly small collection of tools, tips, links and articles in the world of OSINT!
Even though I was back at work, I only spent some time doing some fun stuff in my spare time. I only started writing this all on Saturday, and didn't even know whether I would finish it in time! But it's good to have some time off once in a while. I did finally take some time to play around a with Obsidian, an awesome Markdown note-taking app (and even available on your mobile!). I'm absolutely loving it, and I'm absolutely going to spend more time diving into all the features and plugins it has. But enough of that, it's time for last week's overview of interesting topics:
- Subreddit User Overlap
- Investigating GitHub
- SARveillance
- Non-Mainstream Social Media CSE
- Hidden Photos in Google Maps
Site: Subreddit User Overlap
Steven 'Nixintel' Harris shared a cool site that shows the overlap in users between subreddits. This can give you ideas on other groups to look for information, whenever you are busy diving into the world of Reddit.
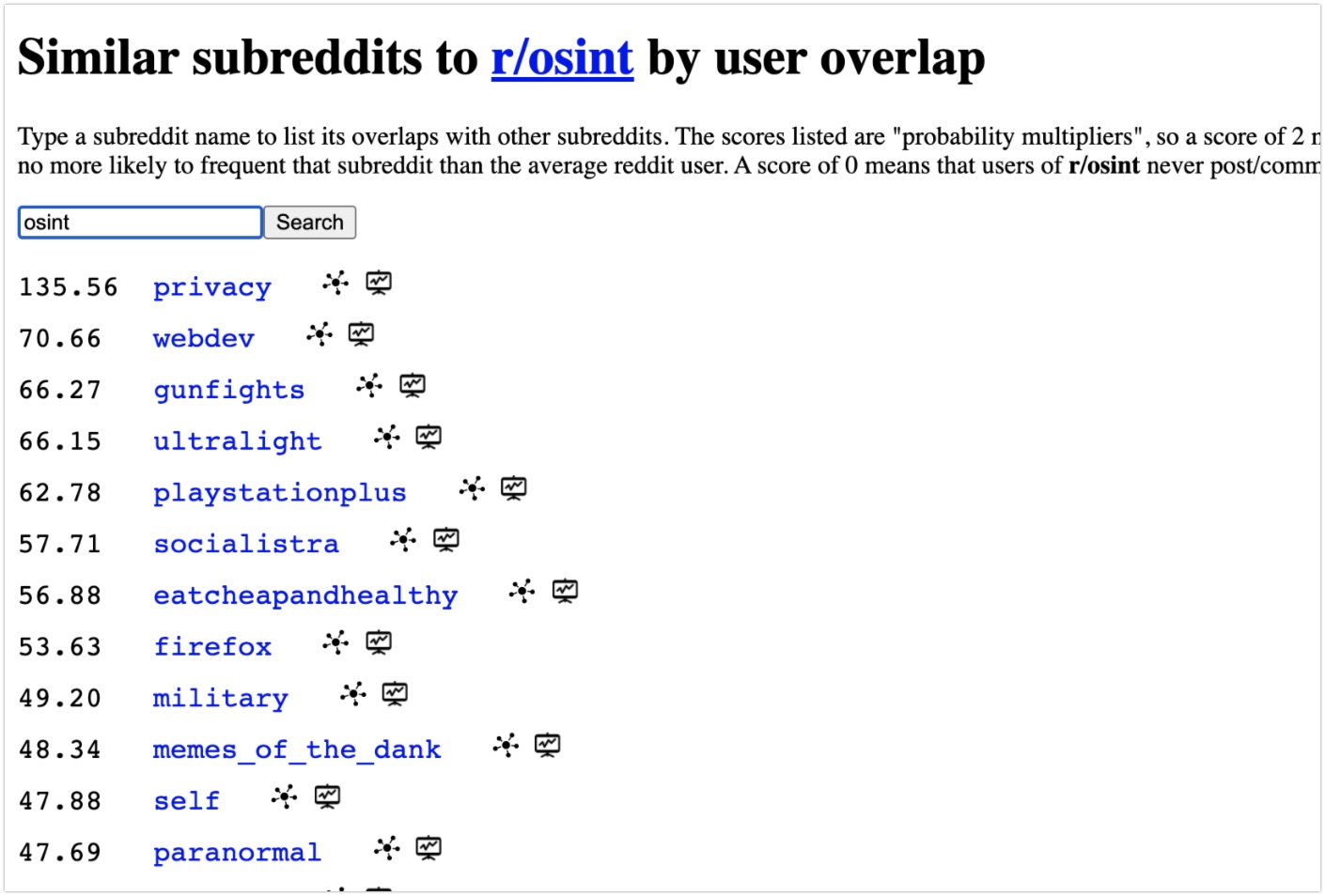
Also make sure to visit the page about the subreddit itself, giving you a wealth of information on the subreddit itself. Do be aware that there is a warning posted that the numbers might not be accurate, but it may give you at least some pointers that can be used within an investigation:
https://subredditstats.com/r/[subreddit]
Link: https://subredditstats.com/subreddit-user-overlaps
Tip: Investigating GitHub
Sinwindie finally had some time again to create another beautiful flowchart, that most of my readers probably already use. This flowchart shows the pieces of information, and possible pivot points, that could be found when investigating GitHub accounts. Another awesome reference card, and I highly recommend you to go through the rest of his GitHub repository!
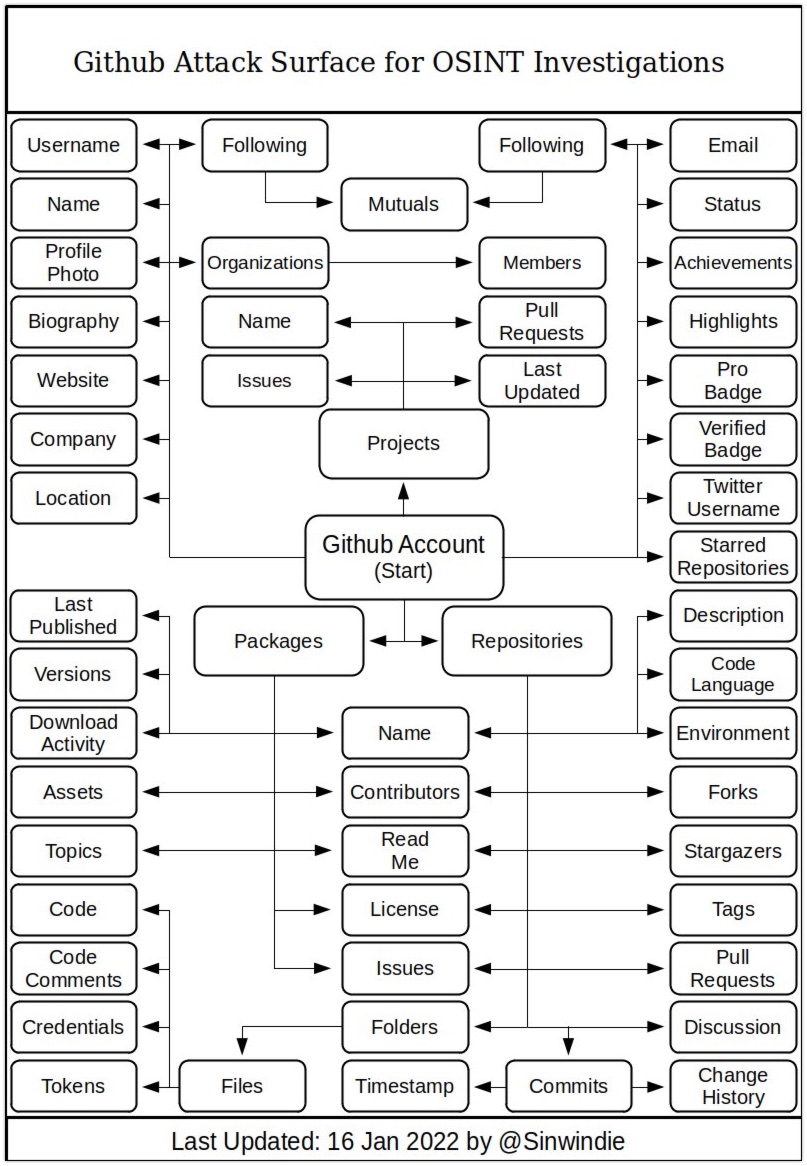
Link: GitHub Repository
Site: SARveillance
Ben Heubl notified me about a tweet from Michael Cruickshank. Because Michael shared a new tool, that enables everyone to have a look at SAR imagery provided by the ESA Sentinel-1 satellites. And the best of it all, the tool will enable you to easily create an animated GIF from any location that is captured by the Sentinel-1!
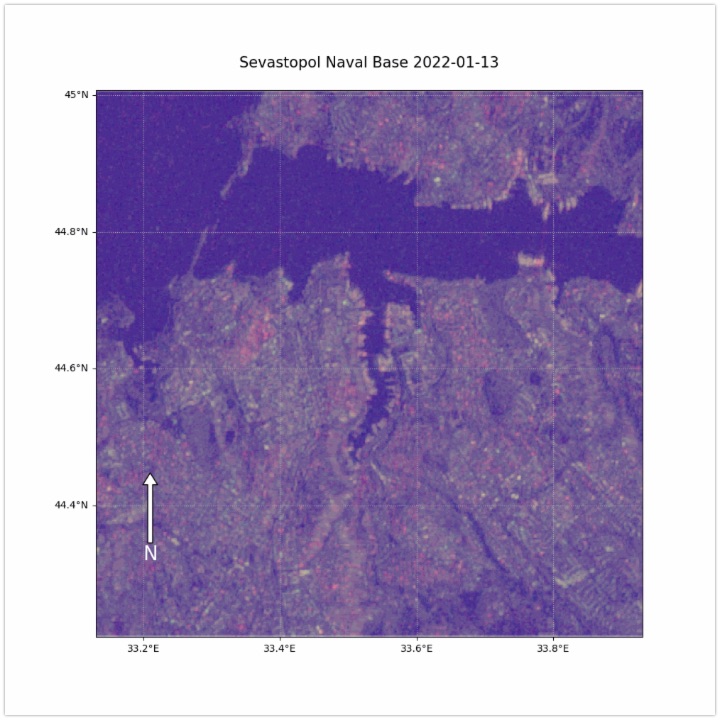
Link: https://share.streamlit.io/mjcruickshank/...
Search: Non-Mainstream Social Media CSE
OSINT Combine has created a new CSE, that focusses on alternative Social Media platforms like Gab, Parler, 8kun and Rumble. With everything that has happened the last few years, this is absolutely a welcome addition to most investigator's toolbox! Thanks for making this.
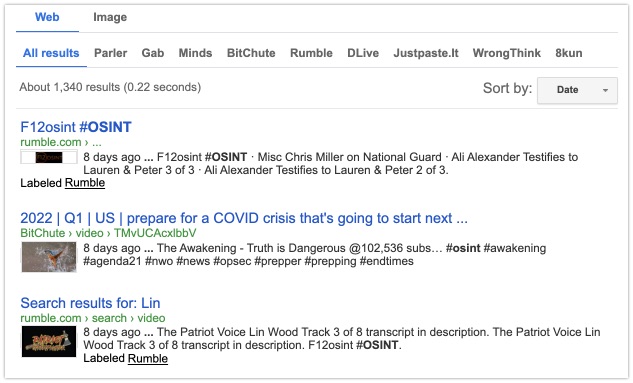
Link: https://www.osintcombine.com/alt-tech-social-search
Tip: Hidden Photos in Google Maps
A great tip that was shared by OSINT_Research, on how to find 'hidden photos' within a a Google Maps location. Twitter user @Pangar-Ban shared his thoughts in a Twitter thread in French, but boils down to this:
- Find the Plus code, via https://plus.codes/map
- Or download them here: https://grid.plus.codes/
- Or use a GitHub tool: https://github.com/google/open-location-code
- Find all the codes within your area of interest
- Run a script to curl all possible endpoints
- Find outliers in file sizes, they contain photos
I'd suggest you practice your scripting skills, and go over the Twitter thread to read it all. It's absolutely worth diving into this when you're looking for images that aren't visible at a first glance.
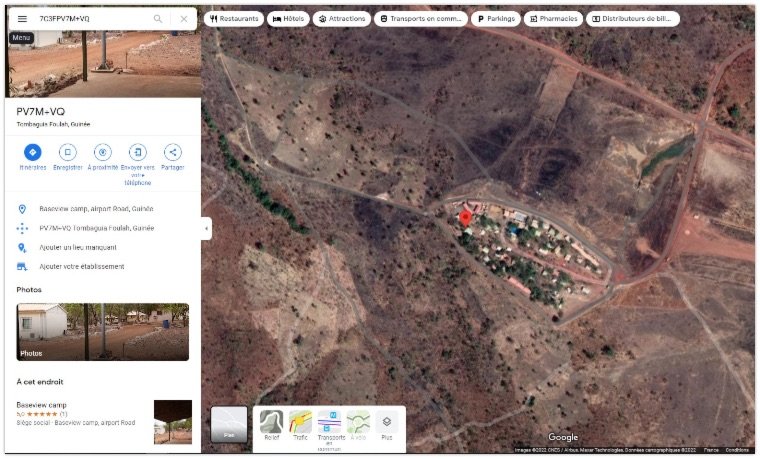
Thread: https://twitter.com/BanPangar/status/1481992641151746052
FUNINT: Poem
White Hat Inspector was in a creative mood, and gave us the following poem in this Twitter thread:
If it's your fault that people went missing, that I would never participate in a @Tracelabs event you would be wishing. You can never hide, I will always find you, whatever you do, you leave breadcrumbs behind you
And if you think my sayings are far from being true, instead of revealing everything, I'll give you a preview. I know where you've been last winter, from the geo/chronolocation quizzes of @sector035 I know the IP address of your printer, from a recent Shodan dorks dive.
You thought u could hide your tinder? Even web archives I can revive Whatever you do my progress you can't hinder OSINT makes me feel alive
You can't any more lurk I told u already it's useless trying to hide No countermeasures work I've read every single @OSINTCurious guide
It's due to your poor operational security, and your sock-puppets' obvious immaturity. You thought you'd hide into obscurity, seems like you have no clue about cybersecurity.
Any michael Bazzell's book, if you had only read, then this poem's twist you would understand. I think it is enough now for this fast-paced course, no go volunteer or donate something, for the National Child Protection Task Force!
Always remember to follow #OPSEC rules, I am White Hat Inspector and I hope you liked my rhyme. Going back to my #DailyOSINT tips and tools, and I thank you for your time!
Have a good week and have a good search!
