Week in OSINT #2024-04
Here is another overview of week 4 from the world of OSINT, covering everything from CTFs to DNS and anything in between!
Lately I have been extremely busy with an education, and for a couple of weeks things won't really improve. So it is possible that a few of the upcoming episodes are slightly shorter than I normally pump out, but I will of course do my best to find at least a couple of interesting things! This week, I have the following topics lined up:
- Hacktoria Contracts
- Phishing Investigation
- Goosint Links
- Easy Dorks
- Wayback Analytics
Site: Hacktoria Contracts
Hacktoria [] has been working hard on their new website, and their new business model. Over the last years they've given us loads of exciting CTFs with great artwork! And while they are working hard on their new and revamped site, they published the first two "Hacktoria contracts"! It is time for you to check out the Latvian Connection, and practice your geolocation, hacking, or decoding skills, and earn badges while doing so!

Link: https://hacktoria.com/category/contracts
Article: Phishing Investigation
This article is an interesting read, and shows how to investigate an active phishing campaign. Manuel Bot [ ] uses external sites like OSINT Industries and Telegram bots to gather information on phone numbers and user accounts. I'm not a huge fan of this myself, since it isn't always possible to independently verify the information, because not all techniques that are used are known to me. But it is still really great to see what tools nowadays can do to help investigators reach their goal.
Link: https://medium.com/@manuelbot59/...
Site: Goosint Links
When it comes to open source data sources on digital components, this website has got you covered! There are loads of categories for you to check out. Do be aware that this is completely different from SOCMINT, so don't simply jump into this without any knowledge. If you do know what it is, and have a need for something, go check out the extensive list of resources available on this site! A lot of people have shared it over the last few months, but I only recently found it thanks to a share by Daily Dark Web [ ].
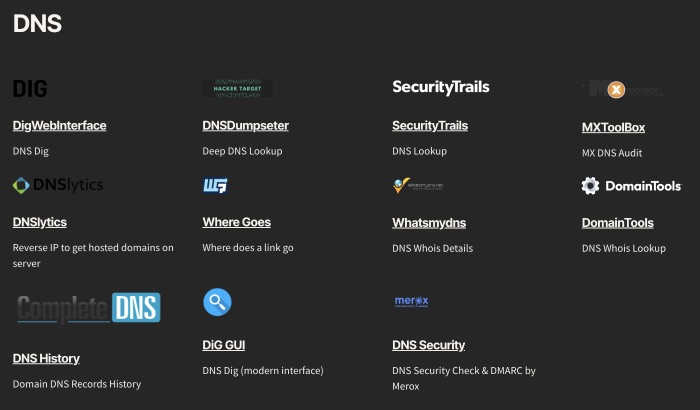
Link: https://goosint.com
Tip: Easy Dorks
And again I feature Manuel Bot [ ], who shared some nice tips by Twitter user Cyber Sudo [] for doing some quick recon on social media profiles. By a few simple Google searches, it is possible to get a quick idea whether a profile might be out there or not. And I think my followers can come up with some more easy to use searches, right? So that's your homework for this week: Come up with some elegant, and useful Google/Bing/whatever searches to find social media profiles, based on usernames, or real names!
Instagram:
site:http://instagram.com "username"
Facebook:
site:http://facebook.com "username" inurl:posts
Here is an example already for Reddit, that gives you profiles of users where "username" is mentioned somewhere on the page:
site:reddit.com/user "username"
Tutorial: Wayback Analytics
Over at Bellingcat [ ] guest writer Justin Clark [ ] wrote an article on how to use the Wayback Machine to retrieve Google Analytics codes, to connect websites to the same admin. With the help of a small Python script, it is possible to query the immense internet archive, and retrieve URLs of domains that used a specific Google Analytics code within a specific period in time. This is another really useful tool in your arsenal!
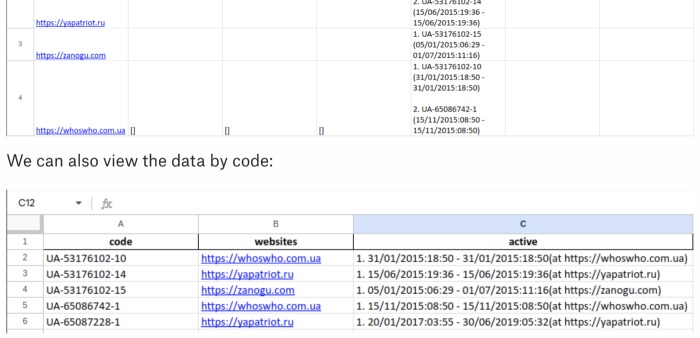
Link: https://www.bellingcat.com/resources/...
FUNINT: This Week's Meme
Last week I had a little talk about exactly this, and since I had this meme already, I think it was a good moment to post it today. And be honest, you probably would look just as smug if realizing it
Have a good week and have a good search!
