Week in OSINT #2022-34
Another collection of tips, tools and tricks on Telegram and some documentation on Darth Maul and drones.
This episode of Week in OSINT features some very exciting topics. Not only do we have some really cool tips and tricks on Telegram, but there's also a new tool to locate Telegram users. Then there is a nice tutorial on how to use cURL, an article on a dark market vendor, and we dive into the world of drones:
- Telegram Tips
- cURL for OSINT
- Darth Maul
- Drones and OSINT
- Geogramint
Tutorial: Telegram Tips
Twitter user hatless1der wrote a blog earlier this month with some good Telegram tips. And the great thing about this post is, that you don't even need to have an account for these tips. From expanding the intro text, to quickly browsing within channels that offer a preview. Some solid tips, with a bonus bookmarklet by Micah Hoffman. Maybe some tips were known already, but I've learned something new too!
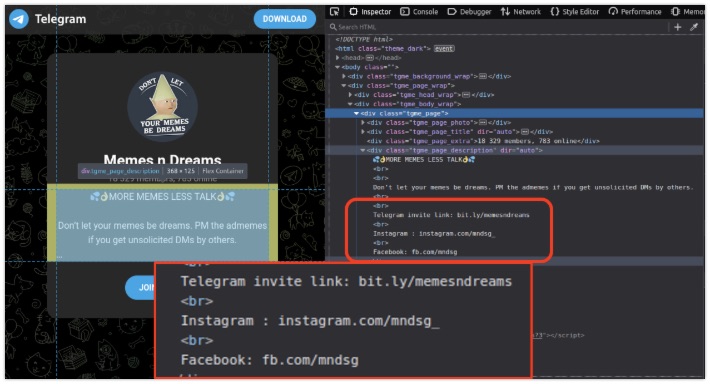
Link: https://hatless1der.com/telegram-osint-basics-5-tips-anyone-can-do-right-now/
Tutorial: cURL for OSINT
Over on Twitter the user Tactical OSINT Analyst shared a long tutorial that he posted over on GitHub. It has lots of tips on how to use cURL to retrieve information from the internet. It might be that he uses iOS, and therefore installs the tool with brew. But if you need to know how to install this tool for your personal operating system, then simply visit the official cURL page over here: https://curl.se/
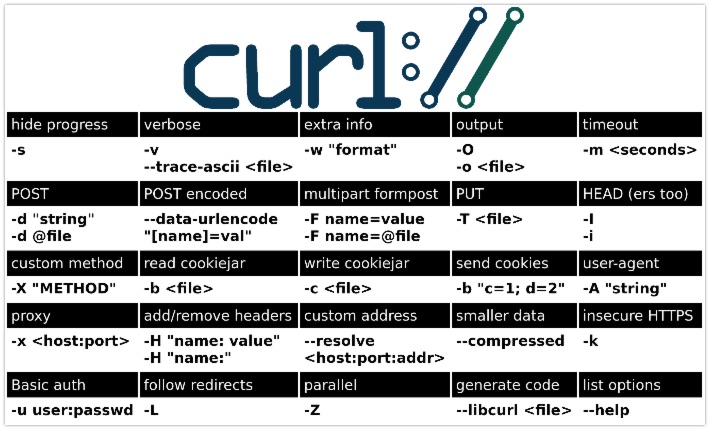
Link: https://github.com/C3n7ral051nt4g3ncy/cURL_for_OSINT
Article: Darth Maul
Bushidotoken has written an article on his personal blog, where he dives into the Dark Maul dark market. I included this article, to show how open source information can be used within threat intelligence. From basic information within Whois registrations, to usernames on forums. These are just a few pieces of information that are the basis of a profile, that will extend over time when more information emerges. In this line of work it's important to document every bit of information, to create an as complete picture as possible.
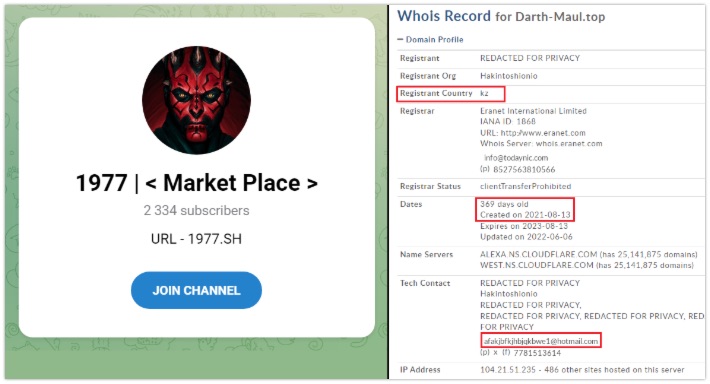
Link: https://blog.bushidotoken.net/2022/08/analysis-of-emerging-darth-maul-ecrime.html
Article: Drones and OSINT
Venessa Ninovic, better known as Intel_inquirer on Twitter, published a blogpost about drones last week. The article is riddles with links to examples, news articles and other blogs. But it also features a set of links that will point you to resources to help you identify drone types, find registration information or even drone footage. And of course you can track drones too, and Vanessa gives an example of that. But if you're really lazy, you can also go over to ADS-B Exchange and click the 'Drone' filter (link). And with that, I'll add another bonus tip: If you are searching for registration numbers of USAF aircraft, then I would suggest you check out the extensive history over at Joseph Baugher's page. And if you want to be really lazy, you can open
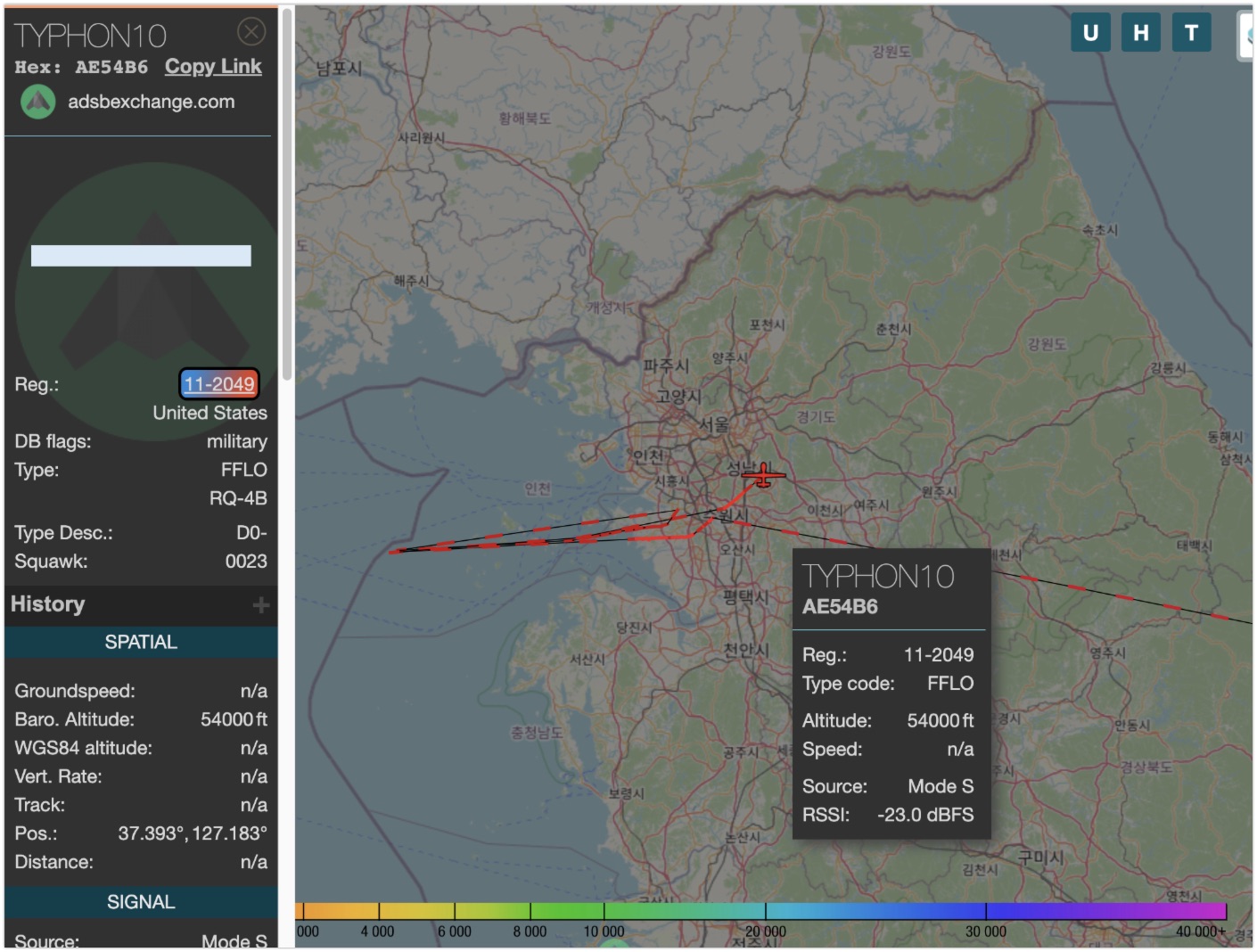
Link: https://link.medium.com/GIdEZnYSKsb
ADS-B Exchange: https://globe.adsbexchange.com/
USAF Serials: http://www.joebaugher.com/...
Tool: Geogramint
Twitter user alb_310 from ProjetFox created an enhanced version of the Telegram nearby tool. After installing and filling in all the information needed, the tool works flawless. With a click on the button, it'll retrieve all users within a distance of 500, 1000, 2000 or more than 3000 meters. And the good thing is, it also stores the results in a JSON file after it finishes. It doesn't offer any searching within the GUI itself, and even though there are no scrollbars, you can actually scroll through the results. But the tool works really easy, and besides showing an avatar to everyone, it doesn't need any other extra rights. So in regard to OpSec, geogramint is a welcome addition to your toolbox!
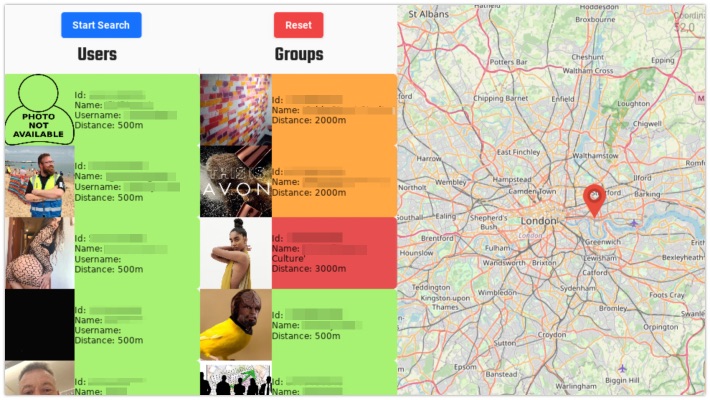
Link: https://github.com/Alb-310/Geogramint
Have a good week and have a good search!
