Week in OSINT #2021-41
Ready for another weekly overview, with topics like: Mapping, searching, datasets, videos and more? Then read on!
Last week has flown past, and before I knew it, the weekend was there. And I didn't have a single topic for this episode. But as I suspected more than enough people had shared some awesome content online to fill this newsletter. And I already have a few topics for some new articles and tutorials. The only issue is: How does one find time to write those articles? Anyone able to OSINT some of that for me? But for now, let's first have a look at this week's topics:
- Mapping Tutorial
- Does This Person Exist?
- Social Media CSE
- Another "Week in..."
- Syrian Datasets
- Layer 8 Videos
- Be Careful What You Search With
Media: Mapping Tutorial
Just before publishing my last newsletter, another awesome video by Benjamin Strick was published. I saw the video, but I simply ran out of time to include it in my last episode. Ben shows you how to run some basic OverPass Turbo queries, how to import them into Google Earth Pro, and what other free tools are available to quickly draw up a map of interesting things.
Link: https://youtu.be/bJkV3l5Haq0
Article: Does This Person Exist?
Twitter user OSINT Shinobi shared an interesting story last week. Over at the University of Caen Normandy in France, they've studied the images generated by "This Person Does Not Exist". By using a so-called "membership attack", they've been trying to establish the source of the images by comparing them with the training data. By finding the source within the training data, it's possible to find out whether someone's image has been used for training purposes without any consent, or provide evidence of copyright infringement.

Link: https://www.technologyreview.com/..
Paper: https://arxiv.org/pdf/2107.06018.pdf
Search: Social Media CSE
Brijesh Singh has been busy playing with Google programmable search engines, or CSE's. He has created a one-stop CSE for social media. With one search, you can view results on Medium. Pinterest, Reddit, Twitter, LinkedIn and more. I know there are loads of CSE's out there already, but it's always good to share extra options.
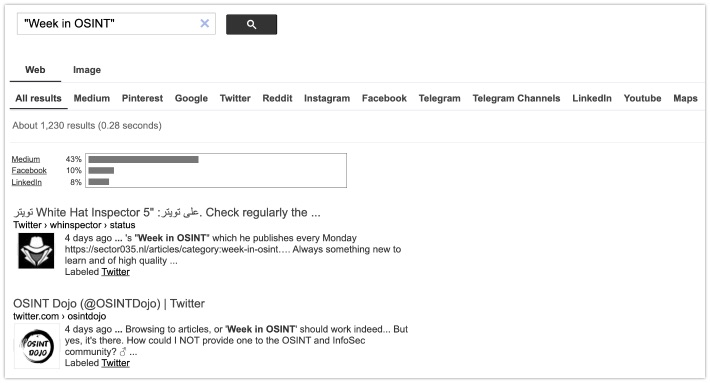
Link: https://cse.google.com/cse?cx=73dda67fd05b4405f
Article: Another "Week in..."
Bleeping Computer is an amazing news platform, but they also seem to have a weekly overview. This isn't really your regular OSINT though, but if you are looking for a weekly overview about ransomware, then this is a really nice site to add to your feed reader. Thanks to Lawrence Abrams you'll stay up to date on the latest news and intel on ransomware.
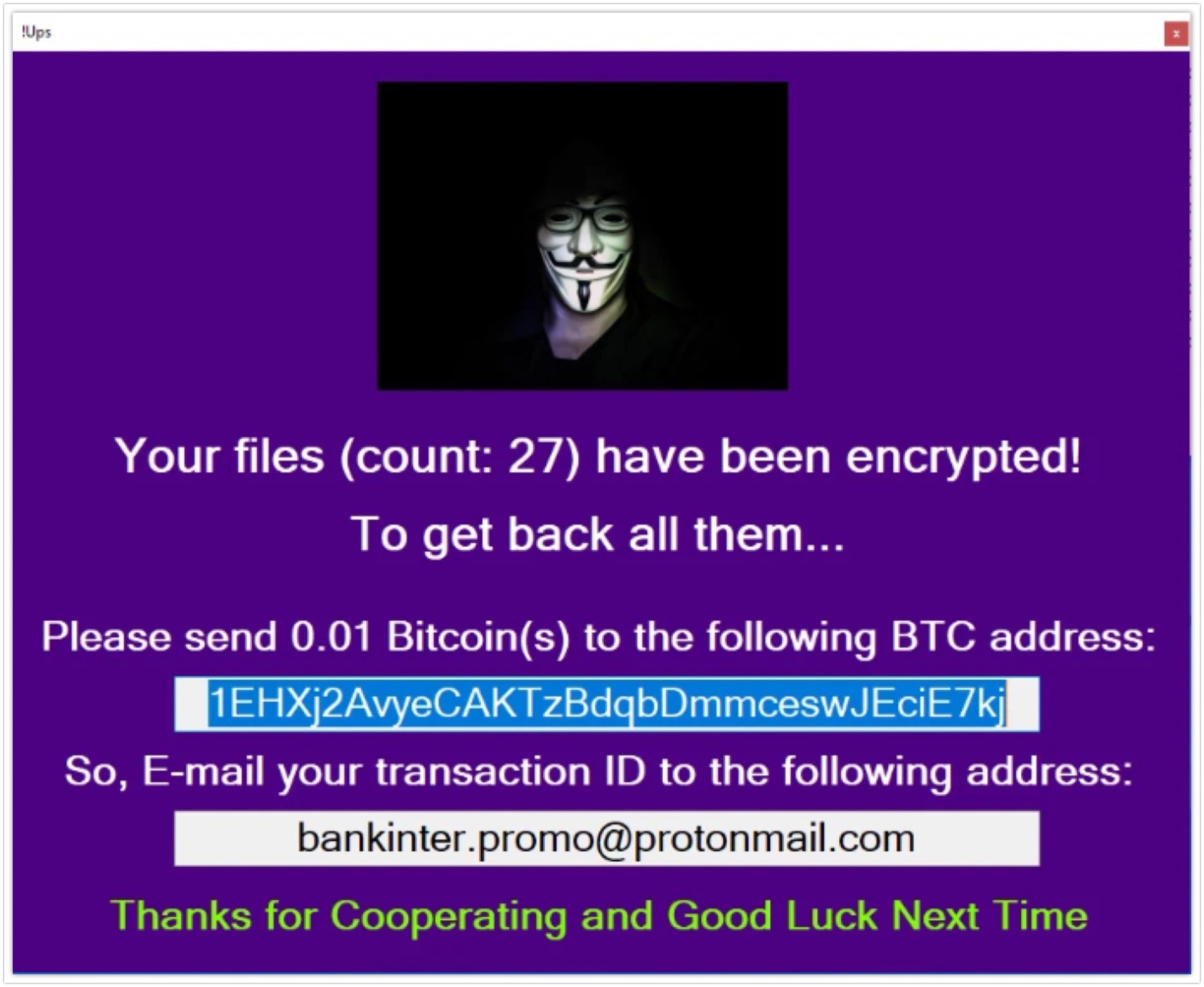
Links: https://www.bleepingcomputer.com/...
Site: Syrian Datasets
OpenFacto is a French organization specialized in OSINT training, fact-checking and assisting others, like NGO's and news agencies. They alerted me to the fact that The Syria Report has opened up two of their databases to the public, and is free of charge: The Official Gazette of the Syrian government and the housing, land and property dataset.
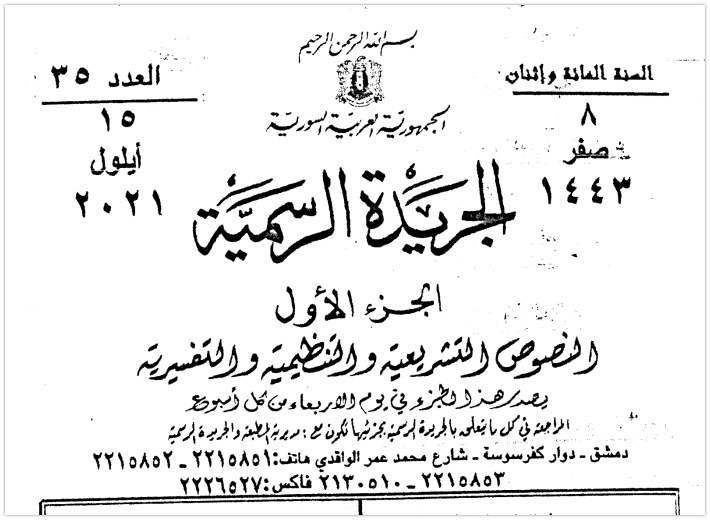
Syrian Gazette (English and Arabic): https://syria-report.com/...
Housing, land and property (Arabic): https://syria-report.com/...
Media: Layer 8 Videos
Earlier this month there was the Layer 8 conference, and recently they've uploaded some videos onto YouTube. Whether it's about social engineering, or mental health, anything that touches open source investigations is game. So sit down, and enjoy these talks. With a little special shout-out to my TOCP colleages Christina Lekati, Rae Baker and Inês Narciso.

Link: YouTube Videos
Tip: Be Careful What You Search With
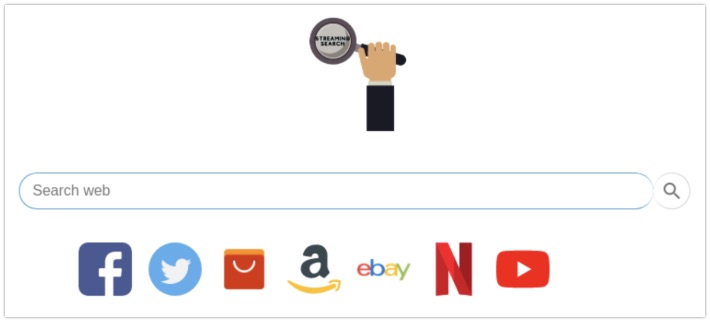
I see loads and loads of links being shared on the TOCP Discord, Twitter, the OSINT sub Reddit and anywhere else. But sometimes things aren't what they seem. For instance, take the website streamingsearch[.]xyz that Twitter user fe_tsoc shared last week. It looks like a very nice website, with multiple ways to search for videos and such. But it actually hides a piece of malware that hijacks your browser, according to multiple sites, like this page over at EngimaSoft. And while checking the website with URLscan.io, I saw there was a distinctive filename being used: cfgnt.json. With that, I quickly found a few other websites that may need to be avoided.
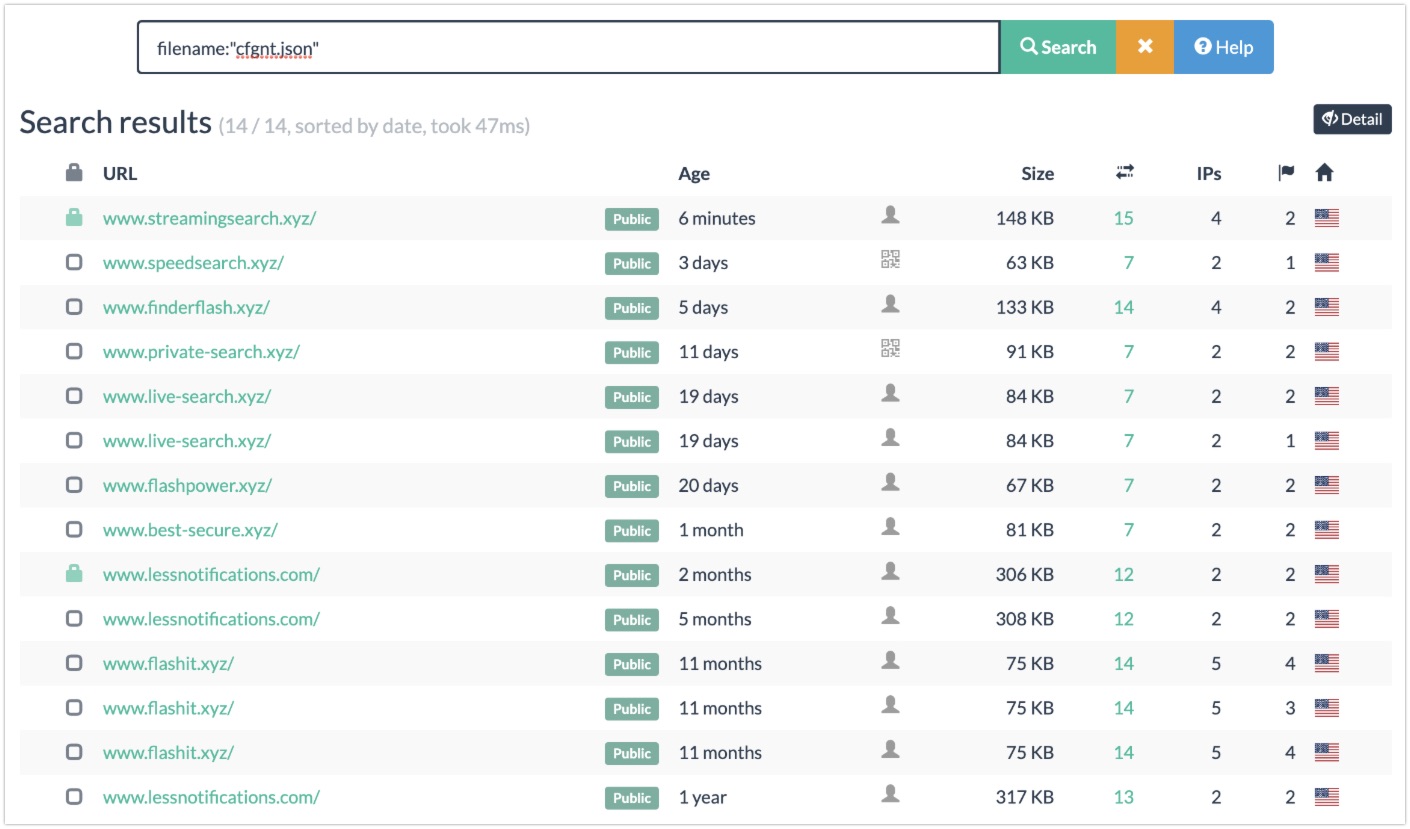
A quick look at the separate scans revealed that the screenshots taken by URLscan showed the same layout and icons, which confirmed my suspicions. So remember: Make sure to do some research before you jump on every opportunity to use a new and novel website. You can use a virtual machine, or a clean research laptop to try things out. And make sure to run an update virus scanner, just in case. Because sometimes things aren't what they seem to be.
Have a good week and have a good search!
