Week in OSINT #2021-04
No matter what area of OSINT you work in, this week I have loads of different topics! From training and telcos, languages and lists to books and Burp!
Welcome to yet another episode of my weekly roundup of OSINT news. Whether you are or know a victim of online abuse, looking for proof, or an ethical hacker that looks for new pivot points. Or maybe you need more information on where a language is used, for geolocation? OSINT is used by many different persons, and this week I'll be sending out some tips for some of these areas of expertise. So enjoy the following topics that I'll be writing about this week:
- Personal Privacy
- Alt-Tech Networks
- Finding Telcos
- Language Flowcharts
- Amazon Wish Lists
- Wayback Machine in Burp
- TikTok Videos
Tutorial: Personal Privacy
This article goes over some basics when it comes to being a victim of online harassment. It shows you how to search, archive and investigate certain social media platforms that are popular. It also provides some basic information about operation security, and how to set-up your privacy settings. Absolutely not a definitive guide, but this is a really good start!
Link: https://www.hackersrepublic.org/culture-du-hacking/digital-raids-osint
Training: Alt-Tech Networks
OSINT Combine will be hosting a free webinar on how to investigate alt-tech platforms and the somewhat unknown platform MeWe. If you are curious on how to tackle new and unknown platforms, do register for this webinar! Time is 6:30am in Canberra, that translates to 19:30 UTC and 2:30pm EST.
We're excited to host another free #OSINT webinar next week on alt-tech platforms & how to investigate MeWe with advanced collection techniques!
— OSINT Combine (@osintcombine) January 30, 2021
Reg here: https://t.co/YUxDMmkN1v
Don't miss out!
Link: https://us02web.zoom.us/webinar/register/WN_VRfFYI9XSPmUoeZ1WVTWSg
Site: Finding Telcos
I didn’t find anything about this in the #osint community but good to know. Here is a website that I used when I worked in telecom https://t.co/fJyZz5Rqjk there you can find the telecom provider of the target for Belgian phone numbers.#cybersec #infosec #socialengineering
— drop (@dropn0w) January 30, 2021
This is an interesting link for people that are looking for the company that holds a phone number in Belgium. In case people are looking for Dutch phone numbers, there's the site of the ACM (Dutch only), a tip that I received long time ago from Aware Online.
Link: https://crdc.be
Link: https://www.acm.nl/nl/onderwerpen/telecommunicatie/telefoonnummers/nummers-doorzoeken
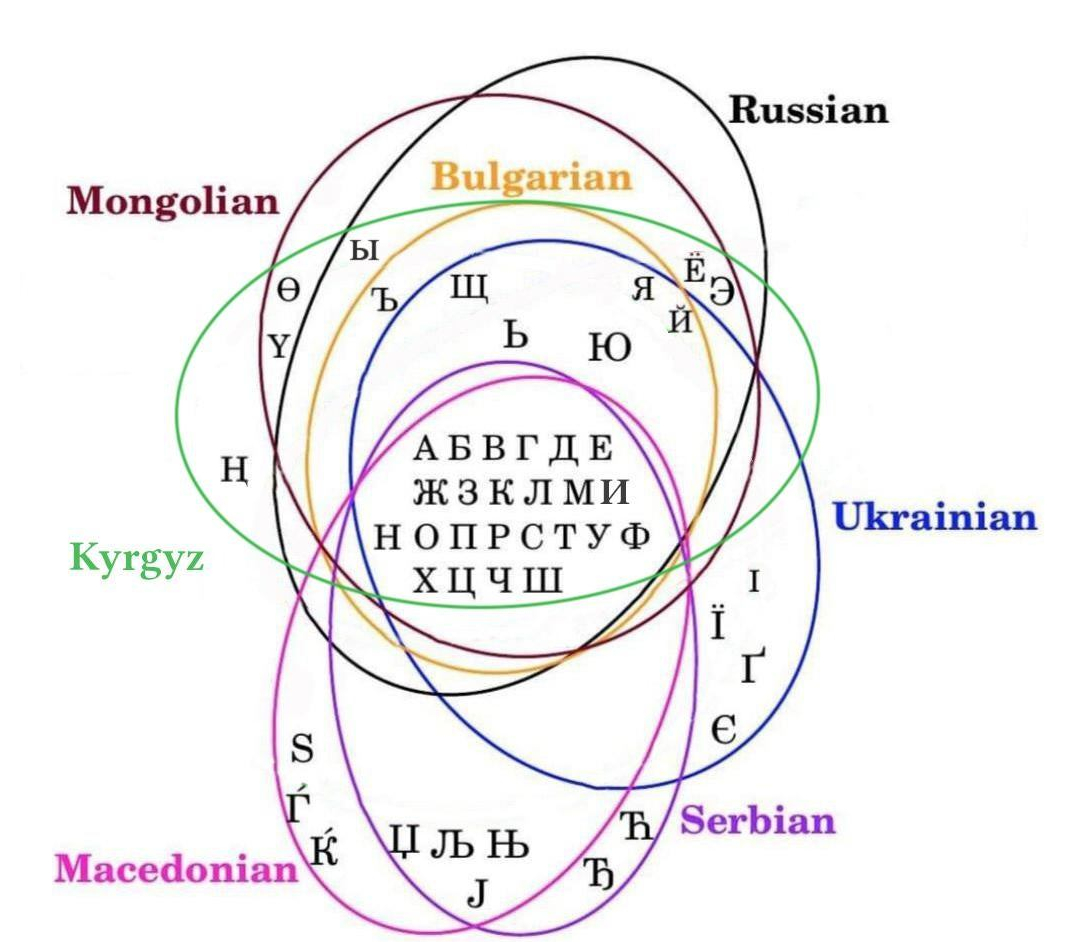
Tip: Language Flowcharts
Lockpicking Pete shared two language flowcharts last week. By going over the characters that are visible, it's possible to distinguish the possible language that is shown. They are included in the extensive GeoGuessr guide, but the original creators are from Duolingo and Reddit.

Tip: Amazon Wish Lists
Joe Gray shared a few Amazon wish lists the other day, and with lockdowns all over the world, this is the perfect time to keep on reading!
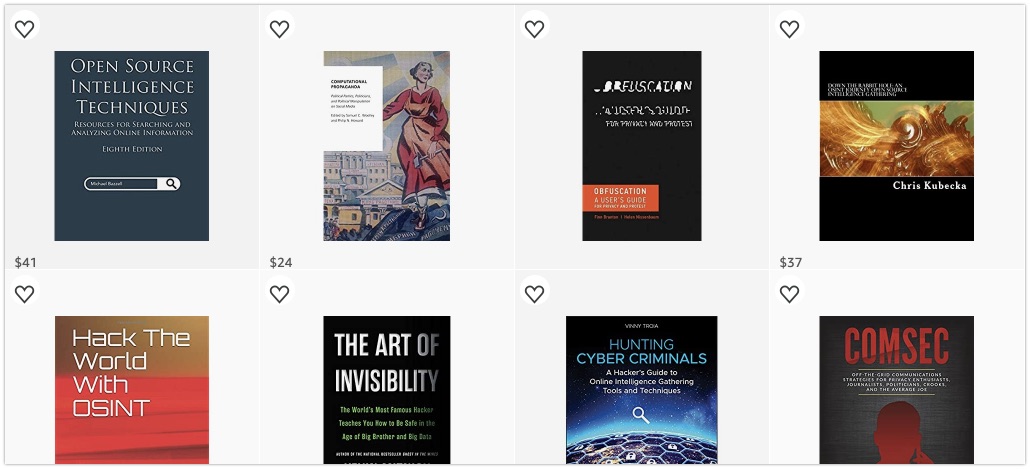
OSINT: https://a.co/1oCofom
GeoINT: https://a.co/8kZgI2Q
Social Engineering: https://a.co/7UXGR8p
Tool: Wayback Machine in Burp
RedHunt Labs released a Burp extension last year that I somehow completely missed. You don't know what Burp is? No worries, this is for the pentesters out there for once. With this extensions it's possible to automatically scan the Wayback Machine for archived pages, to get a list of interesting URL's by passive reconnaissance, instead of hammering the webserver. And besides that, who know what can be found on the Internet Archive that might help you in your current assessment?
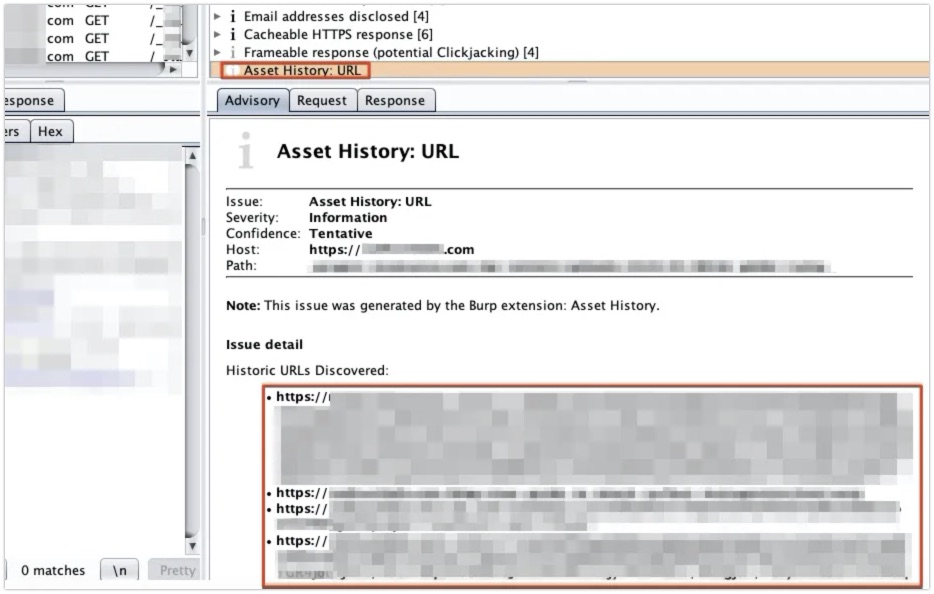
Link: https://redhuntlabs.com/blog/asset-history-burp-extension.html
GitHub: https://github.com/redhuntlabs/BurpSuite-Asset_History
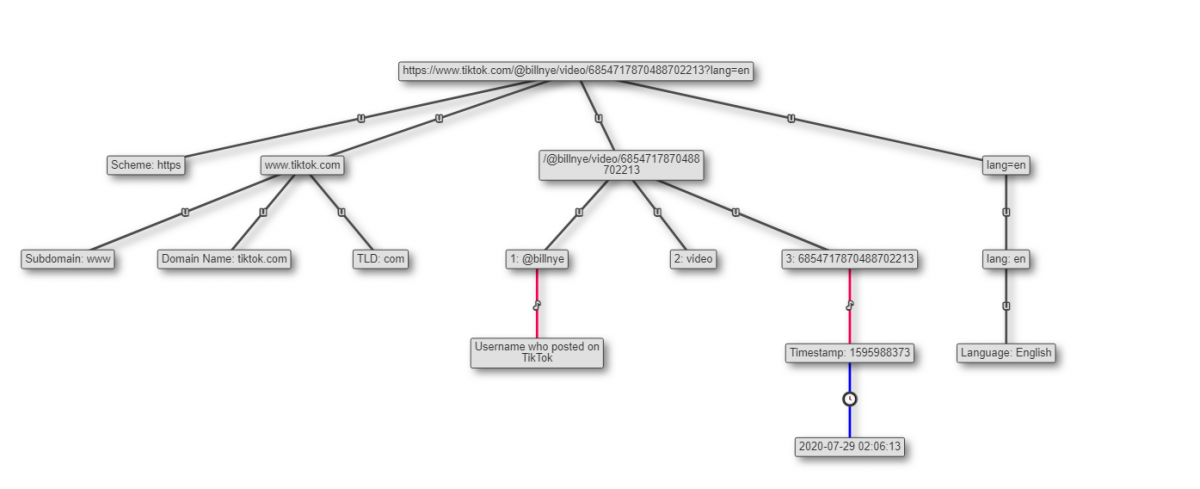
Tip: TikTok Videos
Gonzo was on it again last week with sharing some of his quick tips on Twitter. To download a TikTok video, you can simply go to the 'developer toolbar', search for video-card-browse and you can find the URL to the video. This is especially handy if you don't want to use any extensions or add-on due to trust issues.
⬇️Download TikTok videos:
— GOΠZO (@GONZOs_int) January 22, 2021
- 🎞️ Find and open the video you want to download.
- 🛠️ Open the developer tools (Ctrl + Shift + C).
- 🔍 Search for "video-card-browse".
- 💾 Expand the div and you will see the video url.#OSINT #SOCMINT pic.twitter.com/yHQIZSR7wo
Have a good week and have a good search!
