Week in OSINT #2021-22
Some really interesting links this week: A privacy checker, loads of Telegram links, info on Hunchly and a helpful tool to find related words.
I had to drop a few interesting things this week due to being busy, and I already know I might be struggling to finish the newsletter upcoming week. Because over at The OSINT Curious Project we'll be streaming 5 days in a row next week. I won't join every day, but I usually work on this newletter at the end of the week. Right when I plan to join! But first, let's have a look at this week's topics:
- Awesome Telegram
- Related Words
- Tracking Planes
- Collaborate With Hunchly
- Hunchly Reloaded
- TheMarkup Blacklight
Links: Awesome Telegram
White Hat Inspector sent out a tip about an 'awesome' Github repo: "Awesome Telegram OSINT" by ItIsMeCall911. The list of sites, tools and tutorials on Telegram OSINT is one of the best and most complete I've seen so far. Open the repo and check it out if you're looking for some new sources!

Link: https://github.com/ItIsMeCall911/Awesome-Telegram-OSINT
Site: Related Words
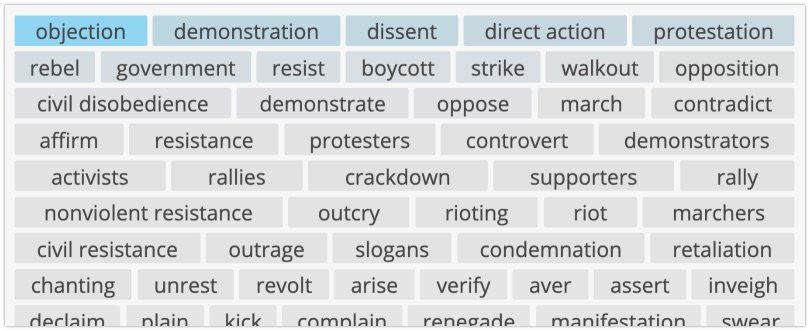
OSINT Techniques shared a website last week that can help you find related words. This is extremely useful for threat intel and need to monitor specific words or terms online. After filling in a word it'll provide you with a huge list of synonyms and related words or terms, where the more promising once seem to be on top. Do also check up the other two related websites that might be useful: ReverseDictionary and DescribingWords.
Link: RelatedWords
Link: ReverseDictionary
Link: DescribingWords
Tutorial: Tracking Planes
Back in September 2019 I had the privilege of working with Emmanuel Freudenthal and give a workshop on plane tracking in Berlin. What we shared in resources in a full day, was not even half of what you can find here. GIJN has written a lengthy article with information on tracking planes, the technical site, finding ownership information and a lot more. This article is a one-stop list of sites, links to tutorials but also examples of how the information is used in real-life investigations. If you are new to this type of investigation, then I do suggest you take a day or so and read each and every article that is mentioned here.

Link: https://gijn.org/planespotting-a-guide-to-tracking-aircraft-around-the-world/
Tutorial: Collaborate With Hunchly
Justin Seitz was asked a question about how it's possible to collaborate with a team when using Hunchly. In this Twitter thread he explains how to use some basic scripting and Google Sheets to send every captured URL to a sheet. And everyone who is configured to access that sheet with the script, will send their URL's to it in real time, thus saving everything in real time as you browse.
So #OSINT folks also wanted to see a streaming sample, which is not great for @zapier so we need to get a little creative with Google Sheets and a bit of code.
— Justin Seitz (@jms_dot_py) May 28, 2021
Goal: Multiple journalists working together with @Hunchly in automatic capture mode.
1.1/n pic.twitter.com/axF7fvGQEa
Link: Twitter Thread
Media: Hunchly Reloaded
Talking about Hunchly, there was a webinar last week about this tool. Justin Seitz doesn't only talk about the desktop version of this tool, but also shows how to import cases created with Hunchly mobile. And the last part of his webinar talks about how to automatically detect and download YouTube videos, while also capturing captions, keywords and more.
Link: https://youtu.be/i_Bs83x-mNc
Site: TheMarkup Blacklight
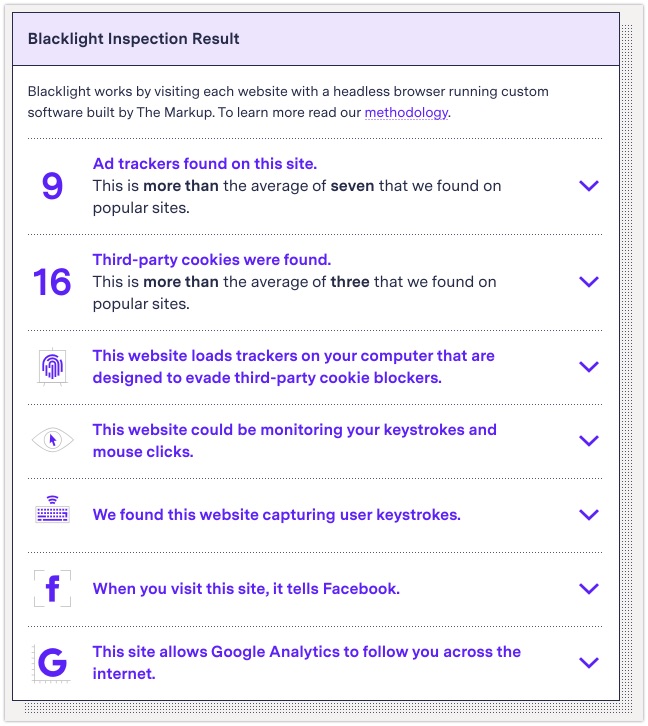
Last week Twitter user UnleashedOsint warned about a link that was shared that contained a session recorder. According to some checks, mouse clicks and movements, page scrolling and even keystrokes were captured. He found it by checking the link with the website Blacklight by TheMarkup, built by suryamattu. This free online tool checks webpages for any privacy invading scripts or apps. This link should deserve a permanent place in your bookmarks!
Link: https://themarkup.org/blacklight
Have a good week and have a good search!
