Week in OSINT #2020-45
Your weekly newsletter with some onions, passwords, searches and other things I've spotted over the last week.
What a week it has been! Besides being busy with work I really wanted to finally start some research with a small team of people, I came up with another personal project on a specific social media platform, I've been creating a bunch of quizzes, and had to find time to squeeze in this newsletter too. I'm really happy the holidays are approaching, I could surely use some OSINT-less time! But first we have the regular business of the Monday, with a newsletter that features the following topics:
- Darktracer
- Password Reset Forms
- Constructing Search Queries
- Dark Markets
- War Stories with Dutch OSINTguy
- Data Collection
Website: Darktracer
Gonzo shared the link to Darktracer.io the other day on OSINT.team. Darktracer.io is a website that runs scans on the dark net to uncover the IPv4 or IPv6 addresses of onion sites out there. The chances are slim that you will have a hit, especially if the site is set-up securely, but it definitely should be on your radar. I haven't had the time to try and figure out who's behind it, but it may be the same people that run the Twitter account darktracer_int, who moniter onion sites for leaked cerdentials (due to the link to South Korea in the Whois). Since it isn't really known who's behind it, or what techniques they use, do make sure to verify all information that you've retrieved via this website.
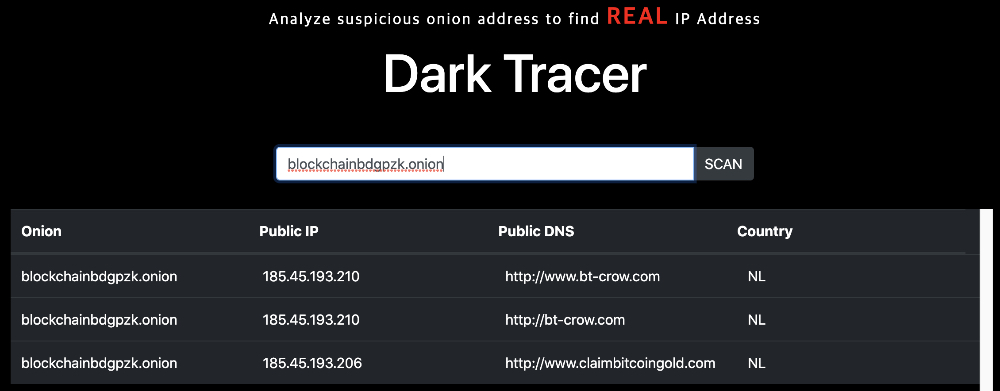
Link: https://darktracer.io
Media: Password Reset Forms
Chris Kirsch has given a presentation on his research on password reset forms a few times before. And this time it is possible to see it on YouTube, from his talk at BSides Boston. A really awesome and insightful talk from someone who has spend an awful lot of time researching this. He dives into what information is given by which platform, how to use breach data to pivot and how to get the most out of the small amount of information given. One small note: Around the 16 minute mark he talks about Twitter, and how it uncovers partial email addresses, but that option has been removed since some time.
Link: https://youtu.be/0BsOEMA9d5s
Article: Constructing Search Queries
Loránd Bodó just launched his website and already has a second article online. This time about how to use boolean operators when searching, and he gives more tips and tricks to enhance your information position. And in the end he touches Tweetdeck in the end, for real-time monitoring of Twitter, and provides some useful links. Can't wait for the next article!
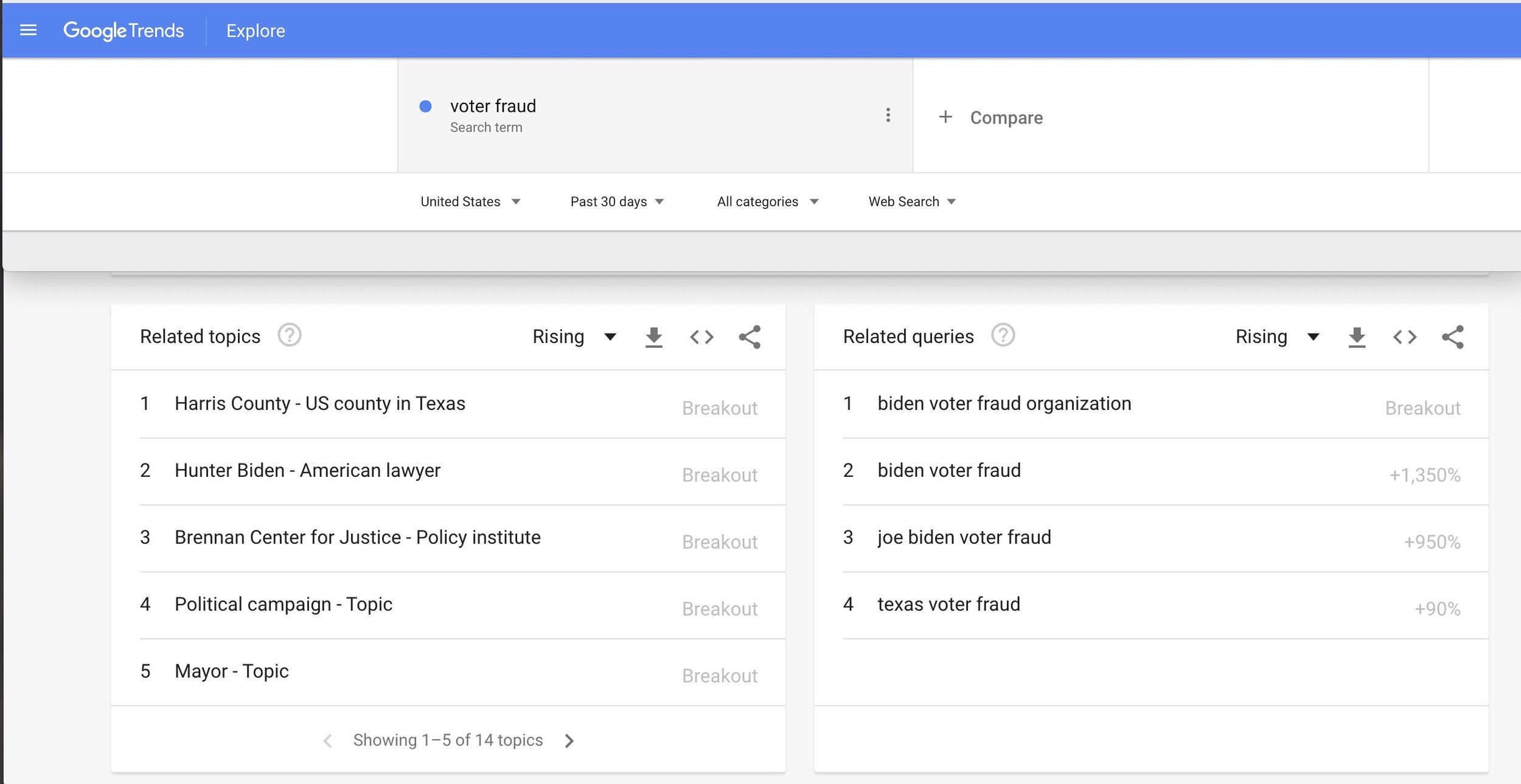
Link: https://www.lorandbodo.com/blog/constructing-searchqueries-osint
Article: Dark Markets
Ciphertrace is a financial investigation company, or as they call themselves a: 'blockchain forensic team'. They have experience in tracking all kinds of cryptocurrency and provide intelligence for investigations, create alerts for addresses used by malicious groups and also wrote this blog about the coming and going of dark markets. It's extremely interesting to read up on how some of these markets dissapear and what the probable reason is.

Media: War Stories with Dutch OSINTguy
"People think you're doing CIA and NSA-kind of stuff ... so you gotta act like a spook, which is nonsense ..."
— ShadowDragon (@ShadowDragonIO) October 29, 2020
Get more #OSINT war stories with Nico Dekens (@dutch_osintguy) and others on the ShadowDragon #podcast. https://t.co/VSUplFOj6J pic.twitter.com/wnXxOmv7iU
There's a new security podcast by Shadowdragon that launched earlier this year, but I didn't have the time yet to listen to it. But when some weeks ago an episode popped up that featured Nico Dutch_OSINTguy Dekens, I had to listen of course! Join him and the hosts for some awesome stories from the digital trenches.
Link: https://podcast.shadowdragon.io/shadowdragon-dutchosintguy-who-needs-heat-crapmaps
Article: Data Collection
Question: Do you know exactly what data an internet company stores? Do you know who has access to your marital status? Or knows your employment status? To illustrate this, Clario has created a list of data points that some well known websites store. And besides it being a good lesson in terms of OpSec, there's an OSINT-y benefit since some pieces of information can be viewed when you create an account on the mentioned platforms.
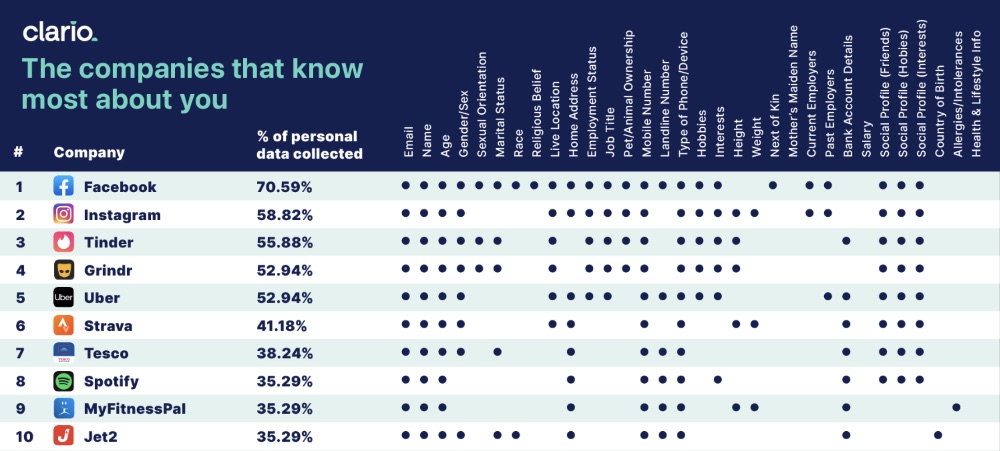
Link: https://clario.co/blog/columns/which-company-uses-most-data/
Have a good week and have a good hunt!
